This thread has generated an amazing number of flagged posts. Gonna slow mode us for a bit.
I’ve been thinking about this story for a day or so now, and while my initial reaction was that it’s ridiculous that Apple lets an AppleID password be reset with just a passcode and a phone, now I’m not so sure. By allowing this, Apple is providing a two-factor (something you have and something you know) mechanism for account recovery that probably works well in the vast majority of cases.
Apple provides a robust method to prevent the types of attacks that are being described in Stern’s article: A long and complex passcode coupled with biometric identification would prevent nearly all shoulder surfing incidents.
Removal of this feature raises the problem of how to provide an account recovery (AppleID password change) method that’s not less secure than what Apple currently provides.
This is a complex issue and there are no simple solutions. Things Apple could do to try to mitigate this include:
-
Make this account recovery method optional. The problem with this is that if it’s opt-in then nearly nobody will use it and if it’s opt-out then nearly nobody will opt out. Apple will effectively be left with either the problem they have, or the problem of providing an alternate secure account recovery method.
-
Require a complex passcode in order for it to be able to be used for account recovery. The problem with that is that people inclined to use low-complexity passcodes will continue to use then and you’re left with the same set of problems that you have if it’s optional in the first place.
-
Apple could require complex passcodes. This would almost certainly cause an enormous outcry by the same people who still use simple passcodes.
-
Apple could require people to acknowledge that they understand that their passcode can be used to reset their AppleID password. This doesn’t solve much other than letting people make a deliberate and informed decision about how they want to balance security and convenience for themselves.
Information security is complex and almost always involves trade offs between competing constraints. It’s also about more than keeping information confidential. Availability is also an aspect of security and is often in opposition to confidentiality. Balancing these things, especially for a large group of unrelated users, is incredibly difficult.
Can Apple do better? Maybe, but I don’t think this is as simple an issue as the Stern story makes it out to be. In the broad community of phone users, the “shoulder surf and grab” attack seems like it’s a relatively small risk, especially since it’s relatively easy to mitigate.
Some of my initial thoughts…
First, the average person would probably do well to learn and understand quite a bit more about social engineering. This particular problem is much more of a social engineering issue than it is a technical issue, and it’s very hard to protect against well-done social engineering with technology.
Second, the average person would probably do well to alter their mindset about their phone. They think of it as something they use to text their friends, but if they use it for banking and such leaving the phone on the counter is the equivalent of leaving their wallet on the counter. We’re used to protecting physical money and things like our credit cards - that attitude about our phones would be valuable.
This would also include basic security precautions like setting the screen lock to a lower number, or getting in the habit of always locking the phone when setting it down. And the more you reinforce those habits when it doesn’t matter, the more you’ll default to them when it does.
Third, tech companies would do well to escalate the difficulty of doing critical things. Asking for your AppleID password to change FaceID, TouchID, your AppleID password, and other crucial account settings would make a lot of sense. You shouldn’t be able to take over somebody’s Apple account just with their phone passcode.
Crimes like this are probably relatively rare except in larger metropolitan areas, but all of the above is good security in general. And the need for good security - especially the need to be conscious of social engineering - is a skill that’s going to be more necessary in the future, not less.
And it’s not that those things are cheap. I haven’t ever handed my phone to a stranger just out of fear they would try and run away with it.
To be fair, if there are reports of criminals abusing the passcode stuff, this is clearly something that Apple should look into, because the victims are not necessarily idiots (and, as a matter of facts, they are paying customers!). But again Apple aren’t idiots themselves so I guess there is some balancing to be done.
I think the main assumption Apple does is that your phone is secured by biometric access, thus everything else that happens inside it is geared towards convenience. As far as I remember, the passcode is not only used to override biometric access: the passcode is needed to decrypt stuff that is inside the secure enclave, hence why it’s needed upon device restart. Perhaps a workaround would be to require FaceID/TouchId after the passcode has been entered but again this is not easy stuff and all the use case scenarios are much more complex.
And I don’t believe that anybody here is an idiot - I just think that people are unaware of how a lot of this security stuff works.
Security is generally some combo of “something you know”, “something you have”, and “something you are”. The PIN for a phone is “something you know”, and if somebody has a camera on you while you’re typing it in it’s “game over” as far as anything on that device that’s not protected another way. Your passcode could be 50 characters of random gibberish and the camera would catch it.
And when it’s a PIN (“something you know”) coming from your phone (“something you have”), that allows you to do the other stuff.
Just thinking out loud, this is mainly about where we draw lines - and I think that’s where the opportunities exist. Apple could potentially require all three (“your trusted device + your PIN + FaceID/TouchID”) to reset your password from your phone, to change your FaceID/TouchID, etc. Or to do weird iCloud stuff.
I think somebody who is able to unlock your phone should generally be unimpeded in their movement around the basic functions of your device. Nobody wants to be re-authenticated for every app, and customers wouldn’t put up with it. But the sections where large, hard-to-undo changes can be made could be secured by the extra biometric, or by requiring the entering of the full AppleID password, or some other theoretically-minimal step that the true user could comply with.
Yes, exactly. Like a home invasion is also a targeted attack on individuals. Or a robbery. Putting yourself in a situation where others can get your keys to your home or your digital home (phone) by just looking under the door mat or looking over your shoulder is a very big mistake that will be abused by bad people. That’s a fact. The problem I see is that the awareness to keep your keys to your house safe is much bigger than the passcode to your phone. The woman in the video says that she did not keep her phone by herself but had it somewhere in her vicinity and didn’t pay attention. Now would you do this with your wallet? I guess no. So the main problem is, imho, that people are not as sensitive when it comes to their phones and data as with their wallet or their keys.
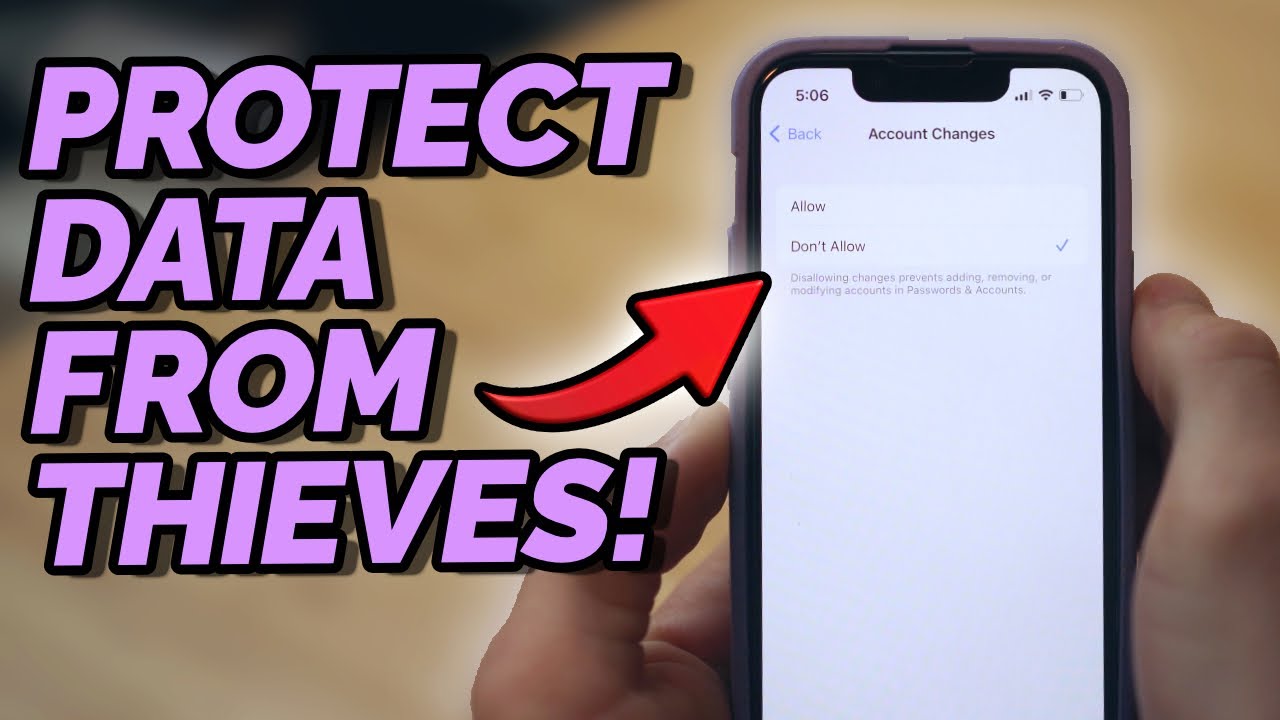
Yes but there are settings that help you prevent this, as the video above shows. And I don’t think people are ignorant because they have simple passcodes. But they are careless if they let their phone unattended lying around in public spaces.
A thief already has 2 hurdles: get the passcode and get the phone.
I’m sorry if I hurt anyones feelings about this. First, my native language isn’t English, so I might say things and they come out very differently or impolite. I didn’t and wouldn’t call people stupid, reckless or lazy. Just unaware or not sensitive enough with their data. There is a reason for that. I’m a very data security sensitive person and I’ve seen a lot in my life. But let’s just look at statistics:
The most used PIN code for bank accounts according to the Guardian is 1234. The second most used is 1111.
NordPass conducted a most breached passwords research in 2021. The 20 most used passwords are 123456.
According to SplashData who are conducting a research like this every year found out that 10% of all used passwords has 123456 as the most used password for the last 6 years.
The National Cyber Security Centre has found out that out of 100 million leaked passwords in 2019 the most used was 123456.
I could go on. This is the reason why I have a different opinion. And it is just that. A different opinion on the matter and not a “blame the user” vibe. People who use 123456 as PIN wouldn’t profit of another security measure or another password or another nagging screen. They would just take the same. And if the same is not allowed it will be 111111.
Thanks to @simonsmark for posting the "Stop iPhone Data Thefts Now!"video. I’ve been reading Apple’s User Guides and security literature for years and never thought to look for important security information listed under “Screen Time”. What was I thinking?
It’s been my experience that most people don’t think about security, digital or physical. I’ve seen them walk into mud puddles while looking at their phone and suddenly veer into a telephone pole at 40 mph. To many “situational awareness” is just something Jason Bourne once said in a movie.
An iPhone should be reasonably locked down right out of the box because people are not going to change. They believe that an iPhone is the most secure and private smartphone available.
And it can be if someone teaches the 1.5 billion non-MPU iPhone users in the world how to make it that way. Or if Apple decides to do it for them.
Of course they would. Take for example the fact that secure institutions do not let you enter, “123456”.
If the iphone ensured better security than a pin, people would have better security.
You mean like, FaceID?!
There’s a lot users can do but either forget or don’t want to because of convenience. I call that the “It won’t happen to me” syndrome.
Both security and privacy are top of my agenda when starting to use a new device. I do spend some time to set it right:
Re. security:
I had to use Outlook for email because of work and it has a faceID lock so I moved all mail there and don’t use the stock mail app.
I password-protect all apps where possible and most also have faceID so there is only minimal impact of user experience. Done this for Signal, Telegram, WhatsApp and all financial apps as well as Devonthink etc.
No passwords saved in iOS/iCloud pw manager. I am using 1Password across all devices.
This way even when someone has the phone open there is little they can do other than checking the weather, the news and call their mother (if they remember the number). SIMs are protected with a password and iPhone Mobile Data Changes not allowed in Screentime.
I agree Apple should bring device security more central to iOS and its setup walkthrough rather than bury various settings in General, Passwords, iCloud, Screentime, Passwords & Security and elsewhere.
Re. privacy:
Apple should do the same for internet privacy and manage use of trackers etc on iOS level rather than have apps “play by the book” or not, though I don’t think this will happen easily so it’s down to user control.
On that note; the same YouTube source of the one posted above, Techlore, have a great setup using iOS with (VPN and) NextDNS which gives you a pi-hole kind of control on your mobile wherever you are. Also a fascinating watch:
It has made mobile browsing faster, no adds, trackers and all done off-device, so no battery impact. Has been a great experience so far.
It depends on what phase of the process you’re talking about.
If we’re talking about the phone unlock, the issue here is that there’s a camera watching - so no password would provide better security against this attack.
If we required a good AppleID password for things like password resets and other changes, that’s a better step logically, and would help somewhat. But ultimately we’re fighting against human nature here. Stricter password requirements frequently lead to passwords on Post-Its or, worse, in Notes docs on the phone.
And that’s the sort of balance we’re looking for. Something that provides additional security without pushing the user in a direction where they compromise their own security and thus negate any benefit they would’ve gotten. ![]()
As a side note, this is one area where 1Password just makes me angry sometimes. It’s theoretically supposed to only require your master password occasionally, allowing you in via FaceID the rest of the time. One trip to the grocery store I had to log into something online, and for something like four or five consecutive password lookups it made me enter my password into my phone every time. The whole reason I use FaceID is so that I don’t have to type in my secure password every time when I’m out in a public place.
As a side note, this is one area where 1Password just makes me angry sometimes. It’s theoretically supposed to only require your master password occasionally, allowing you in via FaceID the rest of the time. One trip to the grocery store I had to log into something online, and for something like four or five consecutive password lookups it made me enter my password into my phone every time . The whole reason I use FaceID is so that I don’t have to type in my secure password every time when I’m out in a public place.
You can set it so it never asks for the master password and use FaceID
FaceID can still be circumvented with the PIN. So FaceID is no more secure than the PIN. The PIN needs making more secure.
I write this with a smile on my face and absolutely no intent to be snarky or sarcastic:
I manage the information security for several thousand people and collaborate closely with people who push that number into the hundreds of thousands; if there’s one thing that’s consistent in a field that changes daily (hourly really), it’s that the folks who are inclined to use use 123456 as a PIN will expend untold energy and display astounding ingenuity to make that wonderfully optimistic statement not true.
I promise you that the moment that they would require more stringent security, you would have the same tech “journalists” who are currently complaining about this issue breathlessly decry how difficult Apple makes it to, “…just pay for my coffee…”
(that last paragraph was a little sarcastic, but it wasn’t directed at you ![]() )
)
I understand that people have a propensity for convenience. But those same people might be thankful that the story in the video is not them telling the story.
I have numerous accounts where you cannot put in well known poor passwords. Other systems will give you a password. Many will keep rejecting your password until it contains what their security policy requires.
Really, Apple allowing “1111” or “1234” demonstrates a pretty shoddy security policy. Especially that this PIN is the gateway to your apple identity.
This “vulnerability” is a system designed by Apple to allow them to assist as many customers as possible. I guess they feel/know there will always be more people who shoot themselves in the foot and need Apple’s help, than people who suffer loss because of this.
AFAIK I’ve done everything possible to secure my phone and iPP. I have nothing in Keychain, and I no longer have anything in iCloud to lose except a few Reminders. I’ve also notified some people of this story and provided them with the information they need to take precautions.
I hope, at a minimum, they will create a recovery key, set up 1Password, and erase everything in Keychain.
This is true, but using FaceID in the example above would prevent the PIN being shoulder-surfed. FaceID theoretically makes the PIN more secure, because it makes it unnecessary to type in the PIN in public environments.
I think there are too many instances when faceID just doesn’t work to be fully trustworthy. I’ve had too many instances when faceID should work but doesn’t, and usually just when I need it.
Exactly. People who are not aware of what they are doing, won’t be with stricter systems. I think it is the wrong way to make security absolutely save for everyone. I don’t expect my key lock producer to lock my house. I have to do it.
Sometimes I don’t like how our society is developing. More and more tasks are being taken away from us, and instead of expecting the simplest things, we expect companies to take our thinking away.
It’s like the McDonald’s coffee cup where a customer goes to court because she burns herself on the hot cup. Is this really the direction we want to go in?
And the worst part is: it’s always the majority that suffers. Because if the problem really affected many people, it would be in all the media.
Then make it more secure by choosing a password instead of the PIN.
No. Those people aren’t aware of what they are doing because if they are, they wouldn’t use 123456 in the first place. Like the woman in the interview they start to think about consequences when it is too late. So they can’t be thankful for something they aren’t aware of.
Studies show, the more complicated a password is and the more special letters you need to put in, the more people get annoyed and start being careless again. Instead of 123456 because it’s forbidden they will use any other simple password like “Password!” or something like this. Or they will write it down on post its and put it on their screen. And so on.
Apple allowing users to choose what they see fit is pure freedom. Why blame Apple for a users fault? Blaming Apple for a user being able to choose 123456 is like blaming a door company for someone who keeps his keys under the door mat.